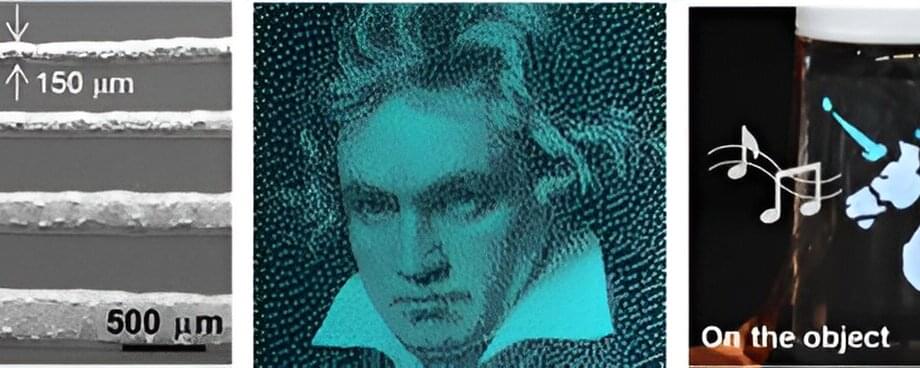
The future of human-machine interfaces is on the cusp of a revolution with the unveiling of a groundbreaking technology—a stretchable high-resolution multicolor synesthesia display that generates synchronized sound and light as input/output sources. A research team, led by Professor Moon Kee Choi in the Department of Materials Science and Engineering at UNIST, has succeeded in developing this cutting-edge display using transfer-printing techniques, propelling the field of multifunctional displays into new realms of possibility.
The team’s research is published in the journal Advanced Functional Materials.
Traditionally, multifunctional displays have been confined to visualizing mechanical and electrical signals in light. However, this pioneering stretchable synesthesia display shatters preconceived boundaries by offering unparalleled optical performance and precise sound pressure levels. Its inherent stretchability ensures seamless operation under both static and dynamic deformation, preserving the integrity of the sound relative to the input waveform.