As the United States, Europe, and China compete to shape the future of the Earth-Moon corridor, strategic advantage will depend not only on launch capacity or lunar infrastructure, but also on advances in quantum technologies. Just as secure systems are critical on Earth, satellites and space-based systems underpin high-value, high-impact operations from financial transactions and navigation to scientific discovery and classified military missions.
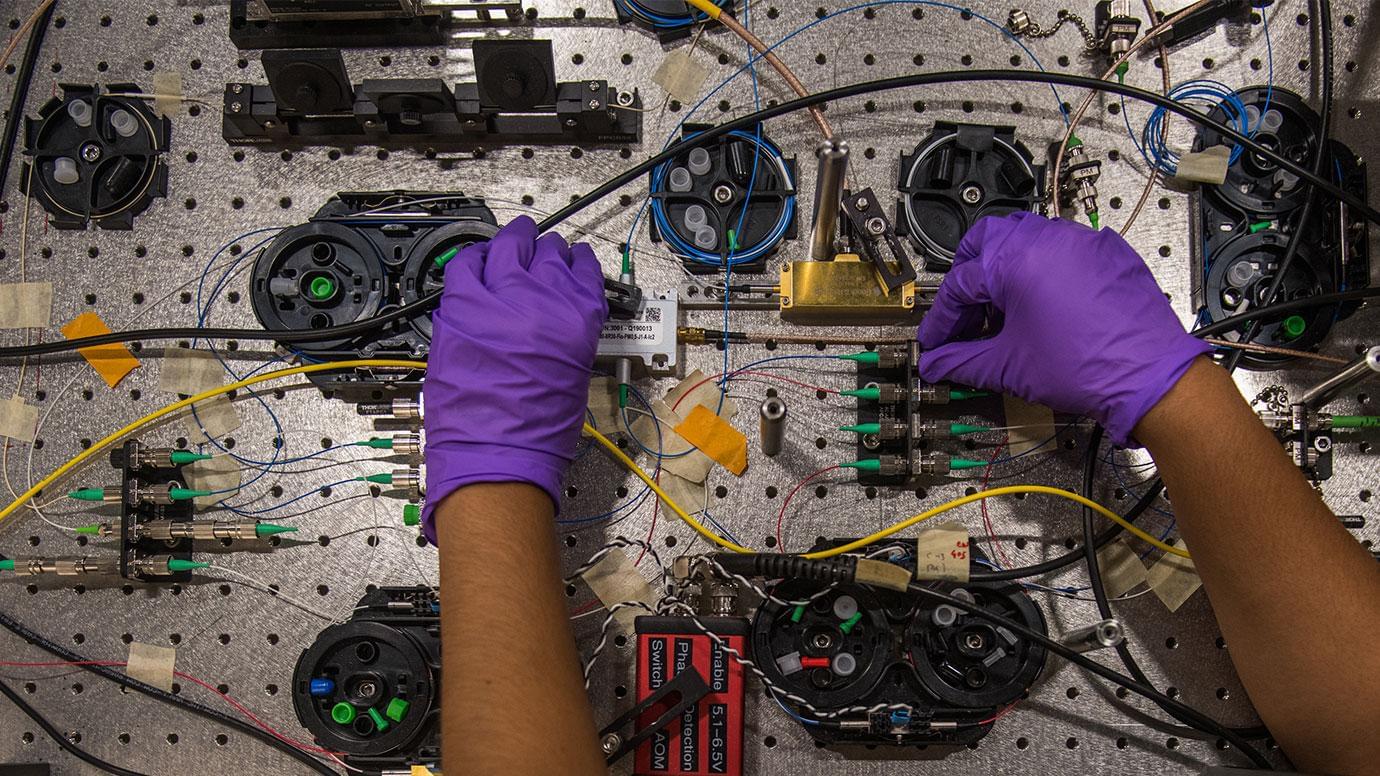
Quantum technologies, which enable new levels of speed, sensitivity, and security, are emerging as critical tools to improve existing extraterrestrial systems. Modern digital communications are secured by encryption built on math problems that are extremely difficult for regular computers to solve, but that sufficiently advanced quantum computers could eventually crack. Quantum communications technologies could add a new layer of protection by making it easier to detect when someone is trying to intercept sensitive information. Quantum sensors can measure position and time with an accuracy that GPS only approximates. Lastly, quantum computers could unlock new capabilities beyond current computational limits, from designing advanced materials to optimizing increasingly complex satellite networks.
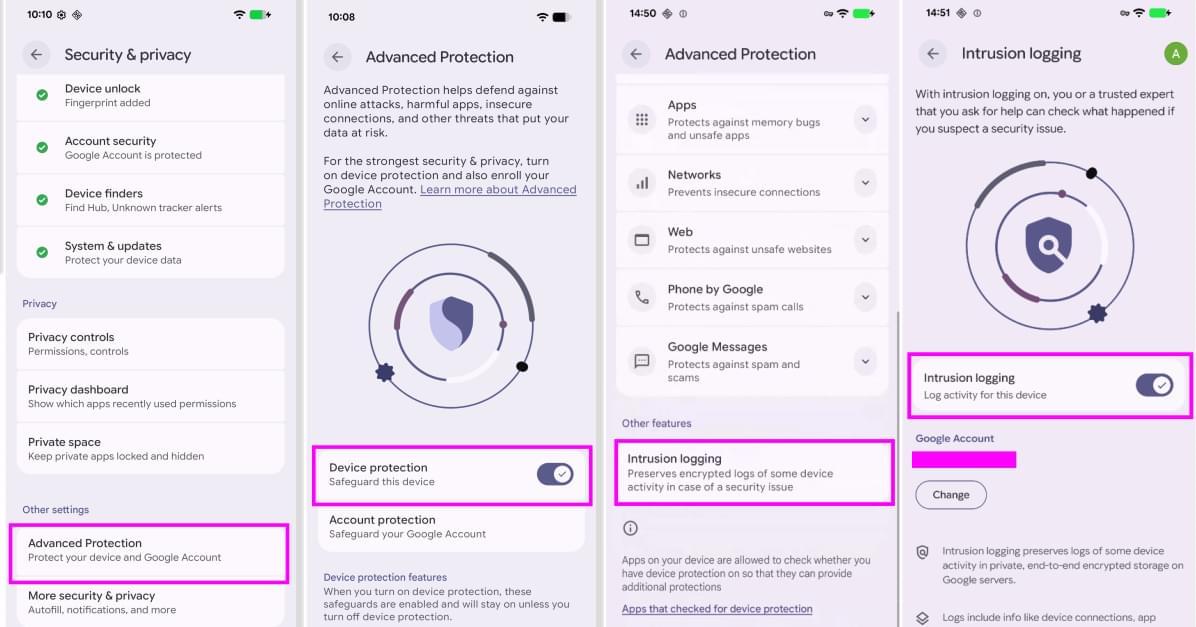
Countries are racing to match their space and quantum ambitions with national strategies. The White House is reportedly drafting an executive order to strengthen US competitiveness in quantum technologies. The rumored draft directs multiple US government bodies, including NASA, to develop a five-year roadmap to expand quantum sensing and networking capabilities. The EU’s 2025 Quantum Europe Strategy highlights “Space and Dual-Use Quantum Technologies” as one of its five strategic focuses, and China’s 15th Five-Year Plan has called for expanding the country’s ground-to-space quantum communications network.