Microsoft creates an AI bug detector that learns to hunt for and fix bugs without being trained on data from real bugs.



Google said Tuesday it has moved to shut down a network of about one million hijacked electronic devices used worldwide to commit online crimes, while also suing Russia-based hackers the tech giant claimed were responsible.
The so-called botnet of infected devices, which was also used to surreptitiously mine bitcoin, was cut off at least for now from the people wielding it on the internet.
“The operators of Glupteba are likely to attempt to regain control of the botnet using a backup command and control mechanism,” wrote Shane Huntley and Luca Nagy from Google’s threat analysis group.

Hackers have taken $196 million from crypto trading platform Bitmart, a security firm said Saturday.
Bitmart confirmed the hack in an official statement Saturday night, calling it “a large-scale security breach” and writing that hackers withdrew about $150 million in assets. However, blockchain security and data analytics firm Peckshield estimates that the loss is closer to $200 million.
Bitmart added in a statement that all withdrawals had been temporarily suspended until further notice and said a thorough security review was underway.


Forget about Mark Zuckerberg, Facebook and all the talk about a metaverse. The real future will be a world that is convenient and scary and fantastical — at least according to futurologists. As this year ends, here’s a glimpse at what life might be like … one day.
Facial recognition is already common for phones, but “In 30 years it’s quite possible that you will not use a key or even a credit card. You’ll use your face or iris to make purchases and open locks. Recognition will be that good,” said Martin Ford, author of “Rule of the Robots: How Artificial Intelligence will Transform Everything.”
“The scary thing, though, will be if someone hacks your biometric data. Right now you can call the bank to change your pin or cancel a credit card. But you can’t cancel your biometrics.”
The Israeli spyware maker in the Pegasus surveillance scandal said Friday it was investigating reports the firm’s technology was used to target iPhones of some US diplomats in Africa.
Apple has begun alerting people whose phones were hacked by NSO’s spyware, which essentially turns handsets into pocket spying devices and sparked controversy this year after reportedly being used on activists, journalists and politicians.
“On top of the independent investigation, NSO will cooperate with any relevant government authority and present the full information we will have,” the firm said in a statement.

Google’s cybersecurity team warns that this is neither the first nor the last time.
Cryptomining is a very energy-intensive process with analysis by the University of Cambridge showing that Bitcoin consumes more electricity than the entire country of Argentina. Now, Google has released a new report stating that malicious cryptocurrency miners are using hacked Google Cloud accounts for mining purposes.
The report is called “Threat Horizons” and it aims to help organizations keep their cloud environments secure.
“While cloud customers continue to face a variety of threats across applications and infrastructure, many successful attacks are due to poor hygiene and a lack of basic control implementation. Most recently, our team has responded to cryptocurrency mining abuse, phishing campaigns, and ransomware,” wrote Google in an executive summary of the report.
“Given these specific observations and general threats, organizations that put emphasis on secure implementation, monitoring, and ongoing assurance will be more successful in mitigating these threats or at the very least reduce their overall impact.”
Full Story:
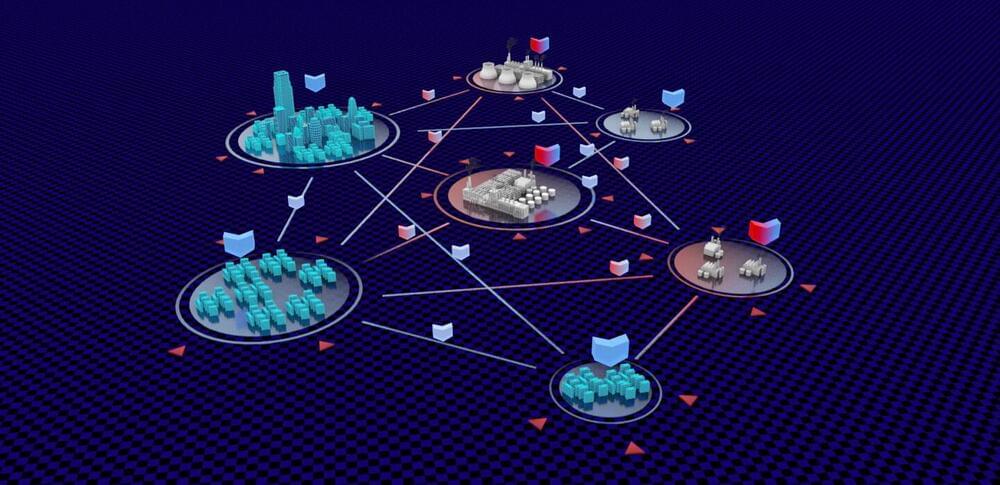
To address the growing threat of cyberattacks on industrial control systems, a KAUST team including Fouzi Harrou, Wu Wang and led by Ying Sun has developed an improved method for detecting malicious intrusions.
Internet-based industrial control systems are widely used to monitor and operate factories and critical infrastructure. In the past, these systems relied on expensive dedicated networks; however, moving them online has made them cheaper and easier to access. But it has also made them more vulnerable to attack, a danger that is growing alongside the increasing adoption of internet of things (IoT) technology.
Conventional security solutions such as firewalls and antivirus software are not appropriate for protecting industrial control systems because of their distinct specifications. Their sheer complexity also makes it hard for even the best algorithms to pick out abnormal occurrences that might spell invasion.