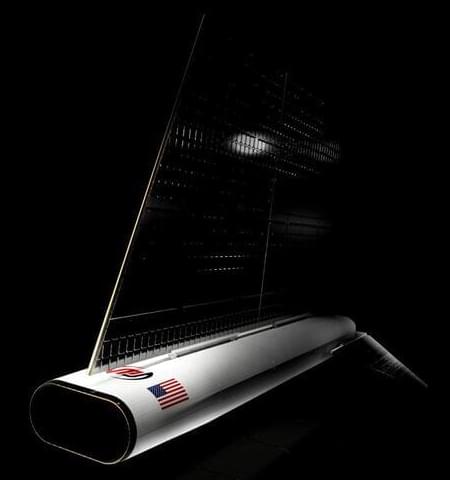
JACKSONVILLE, Fla. (June 17, 2024) – Redwire Corporation (NYSE: RDW), a leader in space infrastructure for the next generation space economy, announced today that it has been awarded a contract from the Defense Advanced Research Projects Agency (DARPA) to be the prime mission integrator for the development of a revolutionary air-breathing satellite that will demonstrate the use of novel electric propulsion systems in very low-Earth orbit (VLEO) using Redwire’s SabreSat VLEO platform. The program leverages Redwire’s worldwide leadership in developing and providing VLEO capabilities.
The strategic significance of VLEO is growing – especially for national security missions. While low-Earth (LEO) and geosynchronous (GEO) orbits are becoming increasingly congested and contested, spacecraft in VLEO operate in a relatively unimpaired environment. Bridging the gap between air and space, VLEO spacecraft fly above airborne anti-access areas while operating significantly closer to the area of responsibility on the ground than existing satellites. Additionally, unlike LEO and GEO, debris in VLEO deorbits in hours or days rather than in decades or more.
“We are proud to be leveraging our SabreSat satellite design to support critical VLEO technology advancements for DARPA’s game-changing Otter program,” said Spence Wise, Redwire Senior Vice President, Missions and Platforms. “As VLEO emerges as a critical domain for national security missions, Redwire is continuing to make investments to support technology innovation and strategic operations in this environment.”