LINKS: https://www.wired.com/story/openai-buy-ai-chips-startup-sam-…i/https:/.…
Category: security – Page 50
45-Year-Old Theory Confirmed: Physicists Shed New Light on the “Invisible” Energy States of Molecules
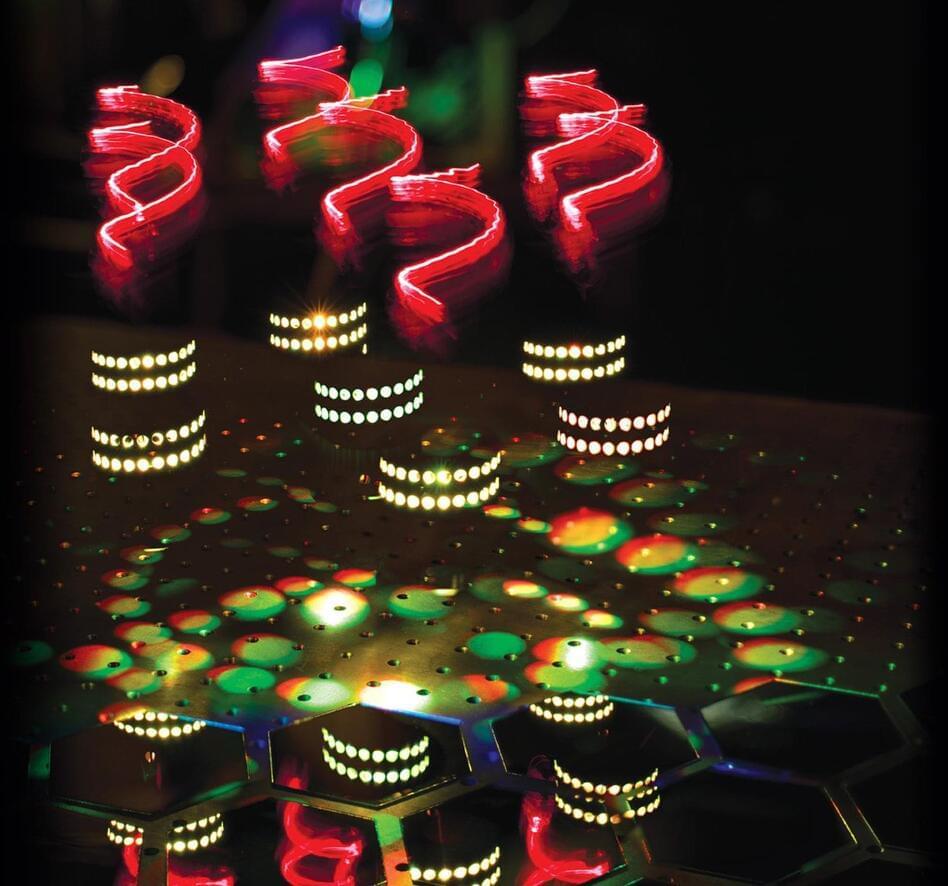
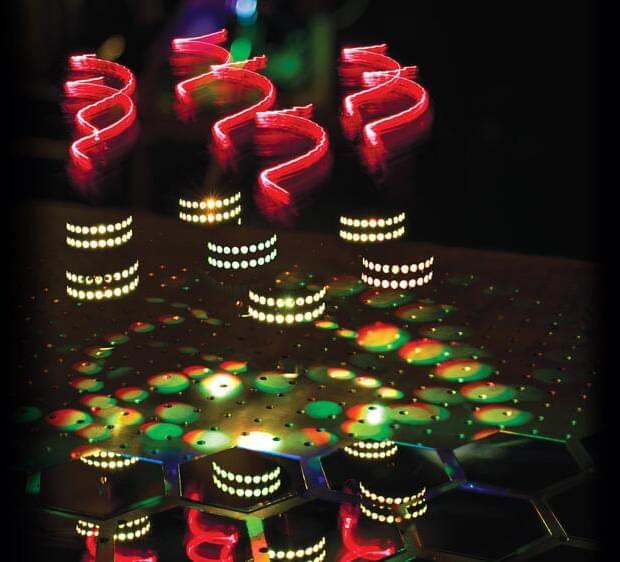
Artistic representation of hyper-Raman optical activity: twisted light (red helices) incident on molecules arranged on a helical scaffold (white dots) produce hyper-Raman scattering spectra (multicoloured light patches) that express ‘chirality’ (patches in spiral patterns and broken mirror). Credit: Ventsislav Valev and Kylian ValevAn international team of scientists, led by physicists from the University of Bath, has demonstrated a new optical phenomenon that could significantly impact various fields, including pharmaceutical science, security, forensics, environmental science, art conservation, and medicine.
Molecules rotate and vibrate in very specific ways. When light shines on them it bounces and scatters. For every million light particles (photons), a single one changes colour. This change is the Raman effect. Collecting many of these color-changing photons paints a picture of the energy states of molecules and identifies them.
Yet some molecular features (energy states) are invisible to the Raman effect. To reveal them and paint a more complete picture, ‘hyper-Raman’ is needed.
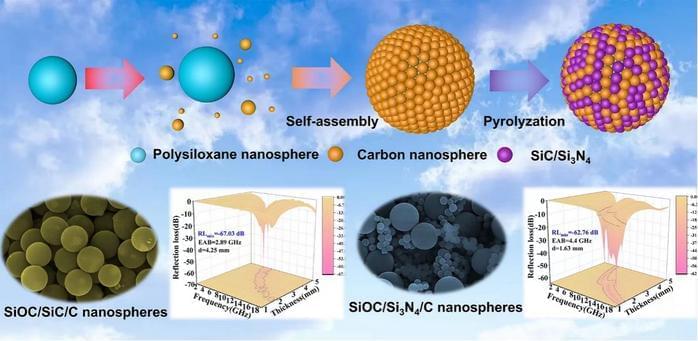
Synthesis of ceramic nanospheres with tunable electromagnetic wave absorption performance
Microwave technology has dramatically progressed, marked by the arrival of the 5G era, owing to the advantages of electromagnetic waves in long-distance, wireless, and high-speed transmissions. However, electromagnetic wave pollution problems such as electromagnetic wave interference and electromagnetic wave radiation are becoming increasingly serious.
Electromagnetic wave pollution not only affects the normal operation of electronic equipment, greatly threatens the information security of the scientific community, but also endangers human health and is a possible cause of cancer and sensitized diseases.
SiOC precursor ceramics have great application potential in electromagnetic protection because of their advantages such as lightweight, high-temperature resistance, and molecular designability. The main challenge of polymer-derived ceramic-based composites for electromagnetic wave absorption is the single loss mechanism, resulting in inferior electromagnetic wave attenuation ability.
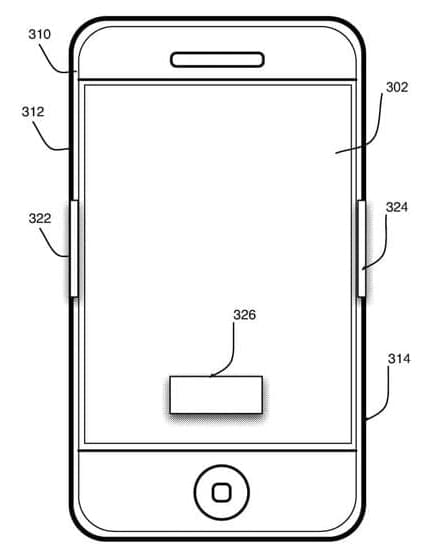
You may soon be able to unlock your Apple devices with your heart
Passwords, Touch ID, and Face ID could all be a thing of the past, as Apple is working on a future where unlocking your devices is as easy as just holding a future iPhone or letting your Apple Watch sense your unique heart rhythm.
Everyone’s heart has a unique rhythm, which the Apple Watch monitors through the ECG app. In a recently granted patent, Apple describes a technique for identifying users based on their unique cardiovascular measurements.
With this technology, you can unlock all your devices if you keep wearing your Apple Watch. Verifying your heart patterns instead of a password or a fingerprint scan increases security and speeds up your identification.

SpaceX planning to land and recover Starship rocket off Australia’s coast
The plan would be to launch Starship from a SpaceX facility in Texas, land it in the sea off Australia’s coast and recover it on Australian territory. Getting permission to do so would require loosening US export controls on sophisticated space technologies bound for Australia, according to the sources, who spoke on condition of anonymity.
President Joe Biden’s administration already has sought to ease similar restrictions within the AUKUS security alliance, opens new tab, a grouping of the United States, Australia and Britain aimed at countering China.
SpaceX, the US Space Force and the Australian Space Agency did not immediately reply to requests for comment.

AI can see what’s on your screen by reading HDMI electromagnetic radiation
Shiver me timbers: Security researchers have demonstrated that it’s possible to spy on what’s visible on your screen by intercepting electromagnetic radiation from video cables with great accuracy, thanks to artificial intelligence. The team from Uruguay’s University of the Republic says their AI-powered cable-tapping method is good enough that these attacks are likely already happening.
Back in the analog video era, it was relatively straightforward for hackers to reconstruct what was on a screen by detecting the leakage from video cables. But once digital protocols like HDMI took over, that became much trickier. The data zipping through HDMI is much more complex than old analog signals.
However, those digital signals still leak some electromagnetic radiation as they transmit between your computer and display. By training an AI model on samples of matching original and intercepted HDMI signals, the researchers were able to decode those leaks into readable screen captures.
Event-driven optical encryption advances information security through neuromorphic imaging
In an era where the internet connects virtually every aspect of our lives, the security of information systems has become paramount. Safeguarding critical databases containing private and commercial information presents a formidable challenge, driving researchers to explore advanced encryption techniques for enhanced protection.
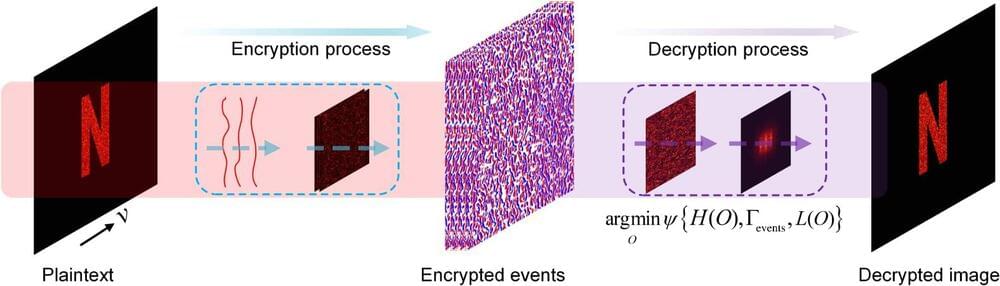
Data encryption, a cornerstone of modern security practices, transforms readable plaintext into encoded ciphertext, ensuring that only authorized recipients can decipher the data using a decryption key or password. Optical techniques have emerged as promising tools for encryption due to their capabilities for parallel, high-speed transmission, and low-power consumption. However, traditional optical encryption systems often suffer from vulnerabilities where plaintext-ciphertext forms remain identical, potentially compromising security.
Reporting in Advanced Photonics Nexus, scientists have unveiled an approach inspired by bio-inspired neuromorphic imaging and speckle correlography. Their innovative technique leverages computational neuromorphic imaging (CNI) to encrypt images into event-stream ciphertexts, marking a significant departure from conventional methods. This method introduces a new paradigm in optical encryption by converting data into event-driven formats, thereby significantly enhancing security and complexity.
Infleqtion Installs First Quantum Computer at NQCC
Infleqtion, the world’s leading quantum information company, announced the installation of a cutting-edge neutral atom quantum computer at the National Quantum Computing Centre (NQCC).
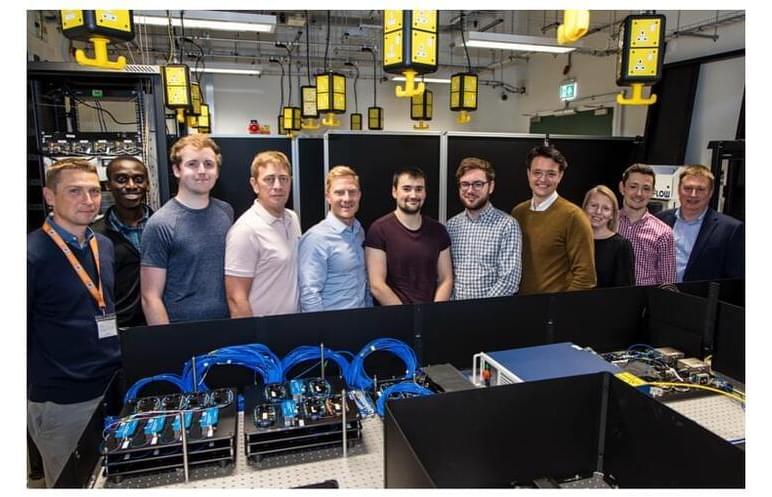
PRESS RELEASE — Infleqtion, the world’s leading quantum information company, is proud to announce the installation of a cutting-edge neutral atom quantum computer at the National Quantum Computing Centre (NQCC). This marks a significant milestone as Infleqtion becomes the first company to deploy hardware at the NQCC under their quantum computing testbed programme. The news comes on the heels of Infleqtion’s rapid advancement in quantum gate fidelity.
Tim Ballance, President of Infleqtion UK, said, “Our recent installation is part of Infleqtion’s dedication to leading facility logistics in partnership with our colleagues at the NQCC. Together, we are establishing crucial infrastructure components such as network infrastructure, safety protocols, and security measures. Infleqtion has completed our second milestone, which includes the installation and in-situ characterisation of primary lasers, optical, vacuum, and electronic subsystems necessary for the quantum computer to function. This accomplishment demonstrates our advanced technology and expertise in the field.”
In parallel to the delivery of the quantum computing testbed hardware, Infleqtion’s quantum software team are working closely on near term applications of quantum computing with NQCC researchers and Infleqtion’s partners Oxfordshire County Council, Riverlane, and QinetiQ. This work includes using Infleqtion’s Superstaq software to apply quantum optimisation to tackle challenges such as traffic management in Oxfordshire. A principal goal of these activities is to demonstrate the practical applications of quantum technology on both a regional and national scale, particularly in areas such as national security and defence.
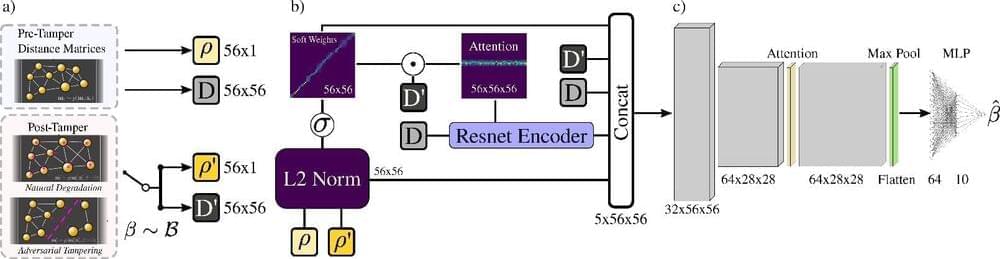
AI-powered optical detection to thwart counterfeit chips
The semiconductor industry has grown into a $500 billion global market over the last 60 years. However, it is grappling with dual challenges: a profound shortage of new chips and a surge of counterfeit chips, introducing substantial risks of malfunction and unwanted surveillance. In particular, the latter inadvertently gives rise to a $75 billion counterfeit chip market that jeopardizes safety and security across multiple sectors dependent on semiconductor technologies, such as aviation, communications, quantum, artificial intelligence, and personal finance.