Quantum computing will break most of the encryption schemes on which we rely today. These five tips will help you get ready.
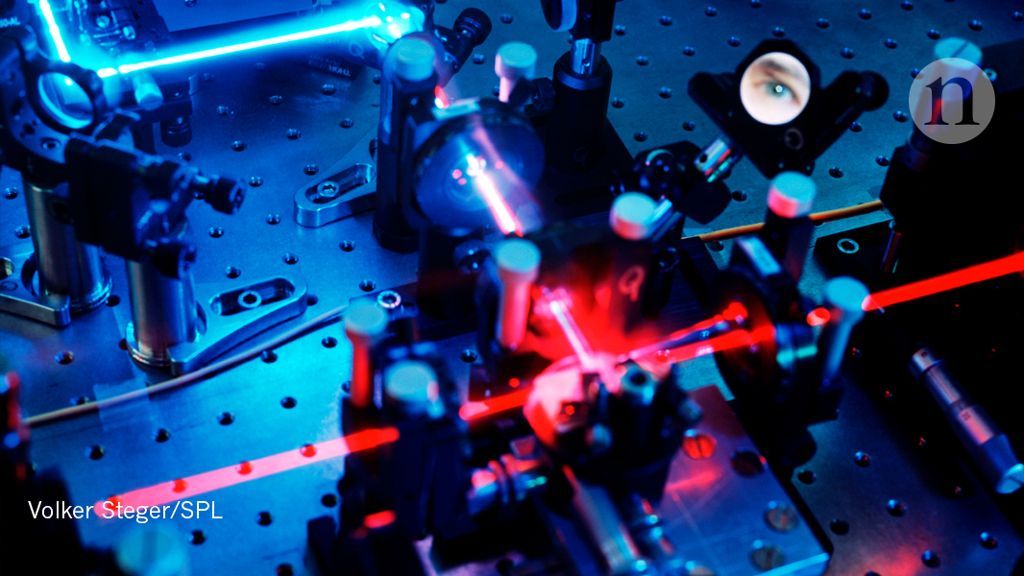
Search on the phrase “quantum computing,” and you’ll find a furious debate. On the one hand, you’ll read breathless articles predicting groundbreaking advances in artificial intelligence, genomics, economics, and pretty much every field under the sun. On the other, you’ll find the naysayers: It’s all hype. Large-scale quantum computers are still decades away — if they’re possible at all. Even if they arrive, they won’t be much faster than standard computers except for a tiny subset of problems.
There’s one area, however, where you’ll find all sides agree: Quantum computing will break most of the encryption schemes on which we rely today. If you’re responsible for your organization’s IT or security systems, and that sentence made the hair on the back of your neck stand up, good. To get ready for a post-quantum world, you should be thinking about the problem now.