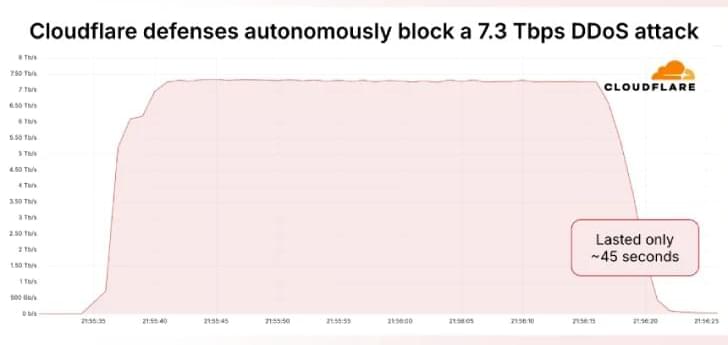
“Hosting providers and critical Internet infrastructure have increasingly become targets of DDoS attacks,” Cloudflare’s Omer Yoachimik said. “The 7.3 Tbps attack delivered 37.4 terabytes in 45 seconds.”
Earlier this January, the web infrastructure and security company said it had mitigated a 5.6 Tbps DDoS attack aimed at an unnamed internet service provider (ISP) from Eastern Asia. The attack originated from a Mirai-variant botnet in October 2024.
Then in April 2025, Cloudflare revealed it defended against a massive 6.5 Tbps flood that likely emanated from Eleven11bot, a botnet comprising roughly 30,000 webcams and video recorders. The hyper-volumetric attack lasted about 49 seconds.