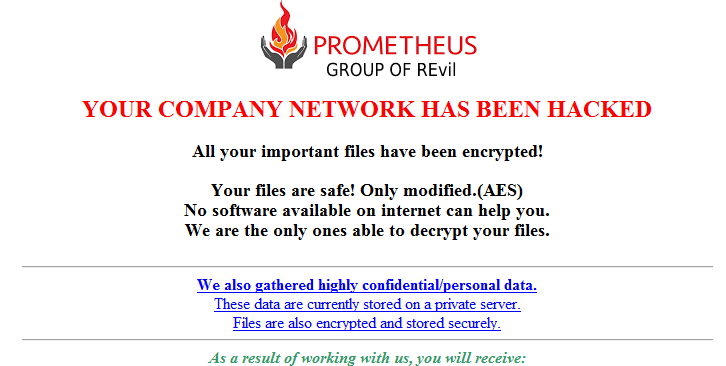
Exploit in the widely used document service leveraged to send malicious links that appear legitimate but actually steal victims credentials.
Threat actors are exploiting Google Docs by hosting their attacks within the web-based document service in a new phishing campaign that delivers malicious links aimed at stealing victims’ credentials.
Researchers at email and collaboration security firm Avanan discovered the campaign, which is the first time they said they’ve seen attackers use this type of exploit in Google’s hosted document service, according to a report published Thursday by Jeremy Fuchs, marketing content manager for Avanan.