It’s “a revolutionary scientific advance in molecular data storage and cryptography.”
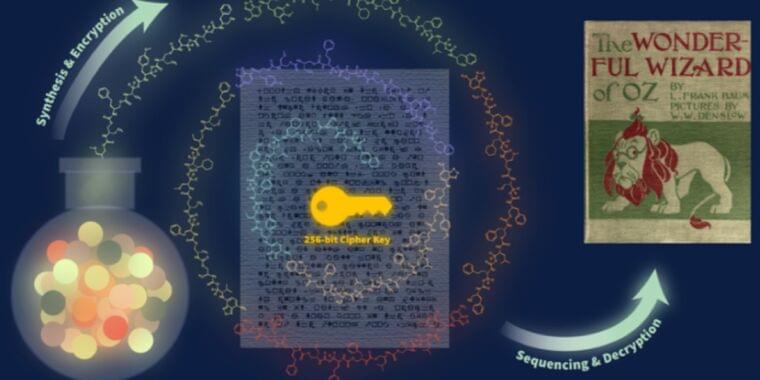
Scientists from the University of Texas at Austin sent a letter to colleagues in Massachusetts with a secret message: an encryption key to unlock a text file of L. Frank Baum’s classic novel The Wonderful Wizard of Oz. The twist: The encryption key was hidden in a special ink laced with polymers, They described their work in a recent paper published in the journal ACS Central Science.
When it comes to alternative means for data storage and retrieval, the goal is to store data in the smallest amount of space in a durable and readable format. Among polymers, DNA has long been the front runner in that regard. As we’ve reported previously, DNA has four chemical building blocks—adenine (A), thymine (T), guanine (G), and cytosine ©—which constitute a type of code. Information can be stored in DNA by converting the data from binary code to a base-4 code and assigning it one of the four letters. A single gram of DNA can represent nearly 1 billion terabytes (1 zettabyte) of data. And the stored data can be preserved for long periods—decades, or even centuries.
There have been some inventive twists on the basic method for DNA storage in recent years. For instance, in 2019, scientists successfully fabricated a 3D-printed version of the Stanford bunny—a common test model in 3D computer graphics—that stored the printing instructions to reproduce the bunny. The bunny holds about 100 kilobytes of data, thanks to the addition of DNA-containing nanobeads to the plastic used to 3D print it. And scientists at the University of Washington recently recorded K-Pop lyrics directly onto living cells using a “DNA typewriter.”