Discover how Beyond Identity’s deterministic security approach eliminates phishing, credential theft, and other cyber threats with passwordless, phish.



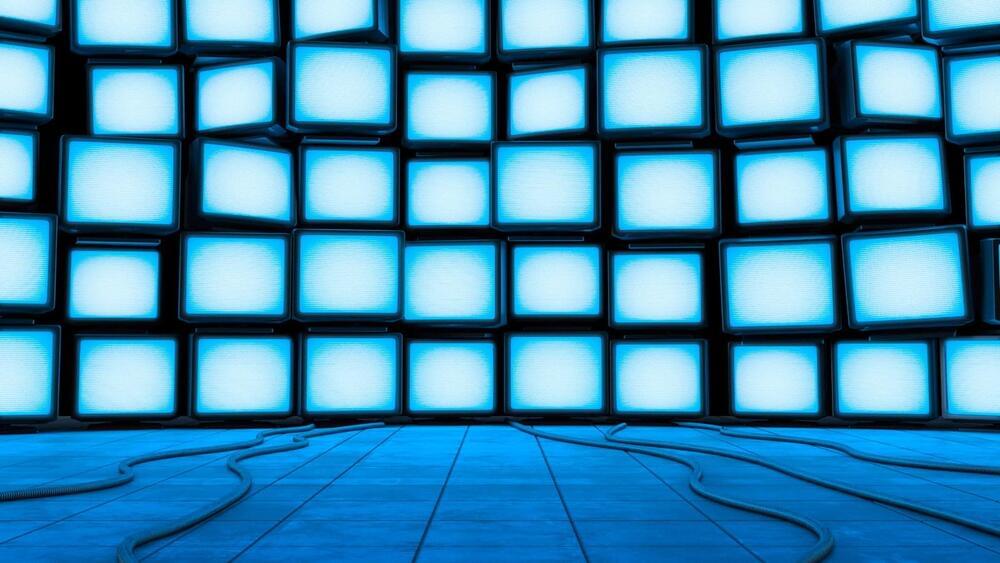
A novel acoustic attack named ‘PIXHELL’ can leak secrets from air-gapped and audio-gapped systems, and without requiring speakers, through the LCD monitors they connect to.
In a PIXHELL attack, malware modulates the pixel patterns on LCD screens to induce noise in the frequency range of 0–22 kHz, carrying encoded signals within those acoustic waves that can be captured by nearby devices such as smartphones.
The researchers’ tests showed that data exfiltration is possible at a maximum distance of 2 meters (6.5 ft), achieving a data rate of 20 bits per second (bps).


Young Consulting has confirmed it lost sensitive data on almost a million people in a ransomware attack that happened earlier in 2024.
The company confirmed the news by sending out data breach notification letters to exactly 954,177 customers, which said it became aware of “technical difficulties” in its computer environment in mid-April 2024.



The three final algorithms, which have now been released, are ML-KEM, previously known as kyber; ML-DSA (formerly Dilithium); and SLH-DSA (SPHINCS+). NIST says it will release a draft standard for FALCON later this year. “These finalized standards include instructions for incorporating them into products and encryption systems,” says NIST mathematician Dustin Moody, who heads the PQC standardization project. “We encourage system administrators to start integrating them into their systems immediately.”
Duncan Jones, head of cybersecurity at the firm Quantinuum welcomes the development. “[It] represents a crucial first step towards protecting all our data against the threat of a future quantum computer that could decrypt traditionally secure communications,” he says. “On all fronts – from technology to global policy – advancements are causing experts to predict a faster timeline to reaching fault-tolerant quantum computers. The standardization of NIST’s algorithms is a critical milestone in that timeline.”