Google reveals COLDRIVER’s new malware families NOROBOT, YESROBOT, and MAYBEROBOT amid rising cyber espionage.


CISA has confirmed that an Oracle E-Business Suite flaw tracked as CVE-2025–61884 is being exploited in attacks, adding it to its Known Exploited Vulnerabilities catalog.
BleepingComputer previously reported that CVE-2025–61884 is an unauthenticated server-side request forgery (SSRF) vulnerability in the Oracle Configurator runtime component, which was linked to a leaked exploit used in July attacks.
The US cybersecurity agency is now requiring federal agencies to patch the security vulnerability by November 10, 2025.
Cybersecurity researchers have uncovered a coordinated campaign that leveraged 131 rebranded clones of a WhatsApp Web automation extension for Google Chrome to spam Brazilian users at scale.
The 131 spamware extensions share the same codebase, design patterns, and infrastructure, according to supply chain security company Socket. The browser add-ons collectively have about 20,905 active users.
“They are not classic malware, but they function as high-risk spam automation that abuses platform rules,” security researcher Kirill Boychenko said. “The code injects directly into the WhatsApp Web page, running alongside WhatsApp’s own scripts, automates bulk outreach and scheduling in ways that aim to bypass WhatsApp’s anti-spam enforcement.”


European law enforcement in an operation codenamed ‘SIMCARTEL’ has dismantled an illegal SIM-box service that enabled more than 3,200 fraud cases and caused at least 4.5 million euros in losses.
The cybercriminal online services had about 1,200 SIM-box devices with 40,000 SIM cards to provide phone numbers that were used in telecommunication crimes ranging from phishing and investment fraud to impersonation and extortion.
In an announcement today, Europol says that the cybercrime service operated through two websites, gogetsms.com and apisim.com, which have been seized and now display a law enforcement banner.
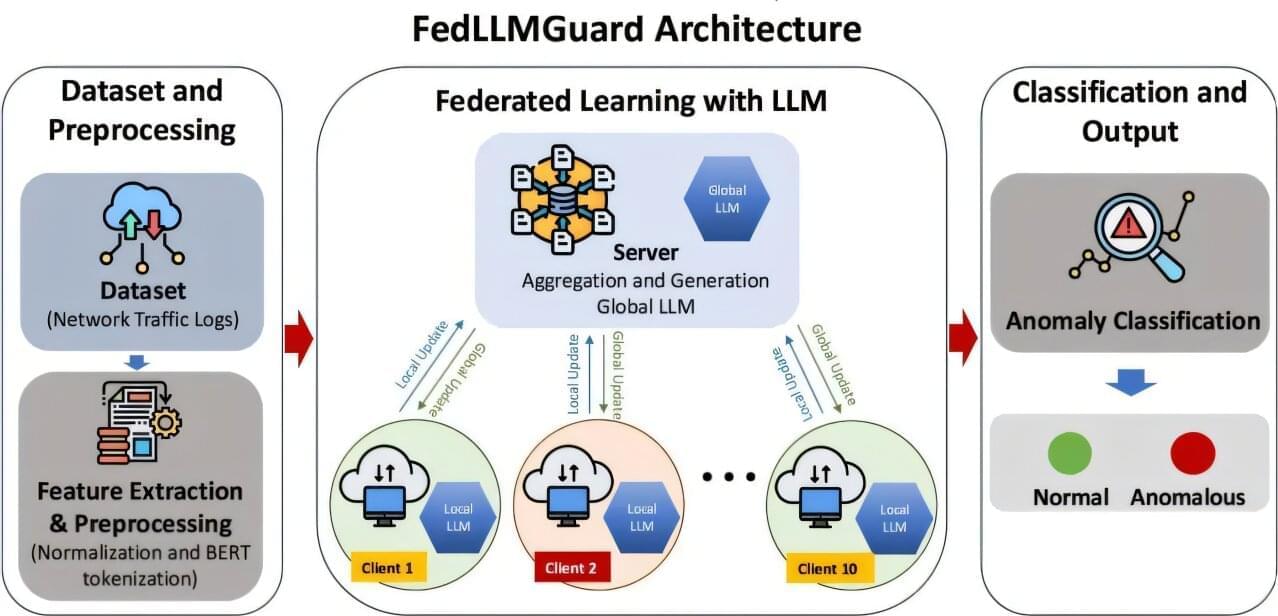
A framework for building tighter security into 5G wireless communications has been created by a Ph.D. student working with the University of Portsmouth’s Artificial Intelligence and Data Center.
With its greater network capacity and ability to rapidly transmit huge amounts of information from one device to another, 5G is a critical component of intelligent systems and services—including those for health care and financial services.
However, the dynamic nature of 5G networks, the high volumes of data shared and the ever changing types of information transmitted means that these networks are extremely vulnerable to cyber threats and increasing risks of attack.