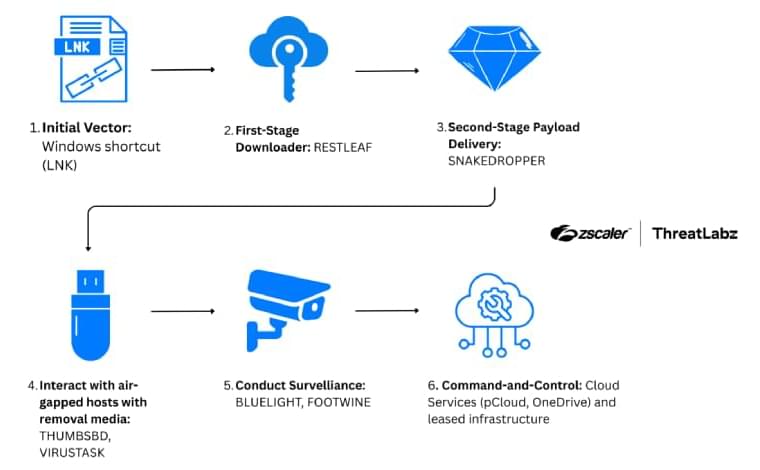
North Korea-linked ScarCruft’s Ruby Jumper uses Zoho WorkDrive C2 and USB malware to breach air-gapped systems for surveillance.

Cybersecurity researchers have discovered four malicious NuGet packages that are designed to target ASP.NET web application developers to steal sensitive data.
The campaign, discovered by Socket, exfiltrates ASP.NET Identity data, including user accounts, role assignments, and permission mappings, as well as manipulates authorization rules to create persistent backdoors in victim applications.



A financially motivated threat group dubbed “Diesel Vortex” is stealing credentials from freight and logistics operators in the U.S. and Europe in phishing attacks using 52 domains.
In a campaign that has been running since September 2025, the threat actor has stolen 1,649 unique credentials from platforms and service providers critical in the freight industry.
Some of the Diesel Vortex victims include DAT Truckstop, TIMOCOM, Teleroute, Penske Logistics, Girteka, and Electronic Funds Source (EFS).

A newly identified cybercrime service known as 1Campaign is enabling threat actors to run malicious Google Ads that remain online for extended periods while evading scrutiny from security researchers.
1Campaign is a cloaking service that passes Google’s screening process and shows malicious content only to real potential victims. Security researchers and automated scanners are served benign white pages.
The operation has been active for at least three years and is managed by a developer using the name ‘DuppyMeister,’ according to a report from data security company Varonis.


Supply chain attacks are now a top cyber threat—SolarWinds and Colonial Pipeline showed how one weak link can cascade across entire sectors.
In my latest article, I examine how AI, 5G, IoT, and quantum computing are expanding both risks and defenses, and share practical steps: zero trust, SBOMs, supplier audits, public-private collaboration, and board-level ownership.
Cyber supply chain security is no longer optional—it’s essential for resilience, innovation, and national security.
Read the full piece: The Cybersecurity Challenges of the Supply Chain https://www.govconwire.com/articles/chuck-brooks-govcon-expe…hain-risks.
#cybersecurity #technology #supplychain
By Chuck Brooks, president of Brooks Consulting International and one of Executive Mosaic’s GovCon Experts