The latest incarnation of the notorious BreachForums hacking forum has suffered a data breach, with its user database table leaked online.




Podcast with Chuck Brooks, Adjunct Professor at Georgetown University and President of Brooks Consulting International — Quantum Computing Report.
Overview In this episode of The Quantum Spin by HKA, host Veronica Combs discusses the intersections of quantum technology and cybersecurity with Chuck Brooks, an adjunct professor at Georgetown University and the president of Brooks Consulting International. Chuck discusses how the evolution of technology, particularly AI and quantum computing, has dramatically transformed cybersecurity. The conversation also touches on the role of CISOs, the integration of new technologies, and the importance of ongoing education and adaptation in the face of rapidly changing technologies. 00:00 Introduction to Quantum Spin Podcast00:34 Guest Introduction: Chuck Brooks00:46 Chuck Brooks’ Career […].

A sophisticated threat actor that uses Linux-based malware to target telecommunications providers has recently broadened its operations to include organizations in Southeastern Europe.
Tracked internally by Cisco Talos as UAT-7290, the actor shows strong China nexus indicators and typically focuses on telcos in South Asia in cyber-espionage operations.
Active since at least 2022, the UAT-7290 group also serves as an initial access group by establishing an Operational Relay Box (ORB) infrastructure during the attacks, which is then utilized by other China-aligned threat actors.

A China-nexus threat actor known as UAT-7290 has been attributed to espionage-focused intrusions against entities in South Asia and Southeastern Europe.
The activity cluster, which has been active since at least 2022, primarily focuses on extensive technical reconnaissance of target organizations before initiating attacks, ultimately leading to the deployment of malware families such as RushDrop, DriveSwitch, and SilentRaid, according to a Cisco Talos report published today.
“In addition to conducting espionage-focused attacks where UAT-7290 burrows deep inside a victim enterprise’s network infrastructure, their tactics, techniques, and procedures (TTPs) and tooling suggest that this actor also establishes Operational Relay Box (ORBs) nodes,” researchers Asheer Malhotra, Vitor Ventura, and Brandon White said.
The malware establishes contact with a hard-coded remote server (“sbido[.]com:2869”), allowing it to steal web browser data, log keystrokes, extract clipboard contents, and other valuable information from the compromised host.
CNCERT/CC and ThreatBook noted that the Black Cat cybercrime syndicate has compromised about 277,800 hosts across China between December 7 and 20, 2025, with the highest daily number of compromised machines within the country scaling a high of 62,167.
To mitigate the risk, users are advised to refrain from clicking on links from unknown sources and stick to trusted sources for downloading software.
A new wave of GoBruteforcer botnet malware attacks is targeting databases of cryptocurrency and blockchain projects on exposed servers believed to be configured using AI-generated examples.
GoBrutforcer is also known as GoBrut. It is a Golang-based botnet that typically targets exposed FTP, MySQL, PostgreSQL, and phpMyAdmin services.
The malware often relies on compromised Linux servers to scan random public IPs and carry out brute-force login attacks.
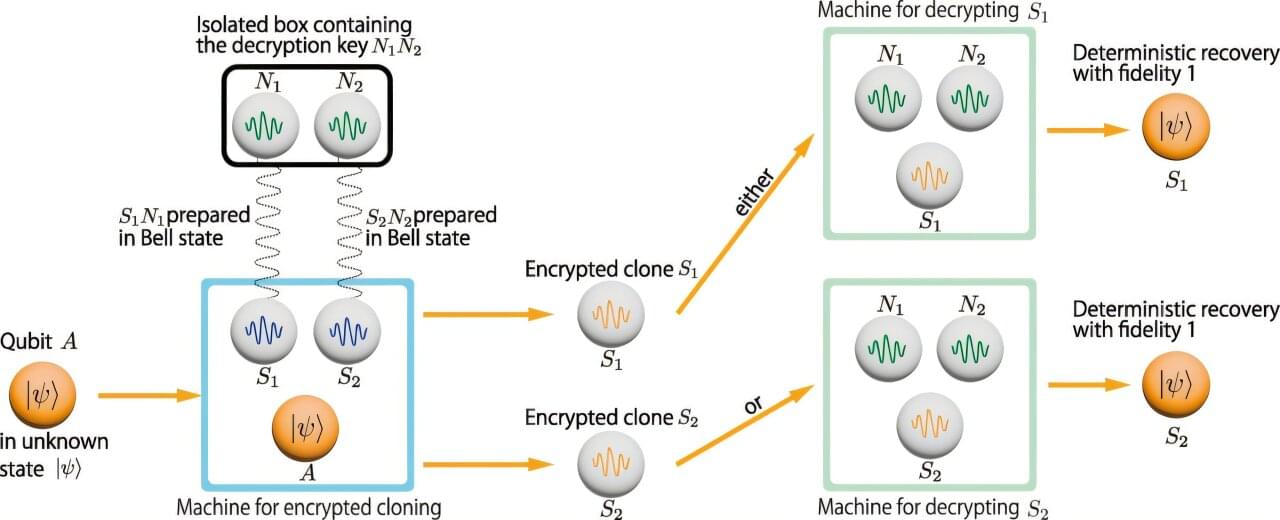
A team of researchers at the University of Waterloo have made a breakthrough in quantum computing that elegantly bypasses the fundamental “no cloning” problem. The research, “Encrypted Qubits can be Cloned,” appears in Physical Review Letters.
Quantum computing is an exciting technological frontier, where information is stored and processed in tiny units—called qubits. Qubits can be stored, for example, in individual electrons, photons (particles of light), atoms, ions or tiny currents.
Universities, industry, and governments around the world are spending billions of dollars to perfect the technology for controlling these qubits so that they can be combined into large, reliable quantum computers. This technology will have powerful applications, including in cybersecurity, materials science, medical research and optimization.
A new PHALT#BLYX campaign targets European hotels using fake Booking.com emails, ClickFix lures, PowerShell, and MSBuild to deploy DCRat malware.