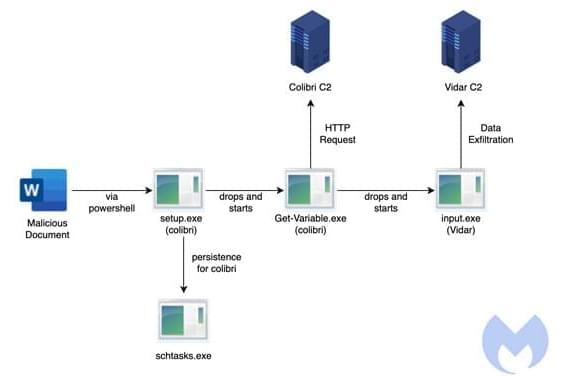
Phishing attacks are cyber-attacks through which criminals trick users into sending them money and sensitive information, or into installing malware on their computer, by sending them deceptive emails or messages. As these attacks have become increasingly widespread, developers have been trying to develop more advanced tools to detect them and protect potential victims.
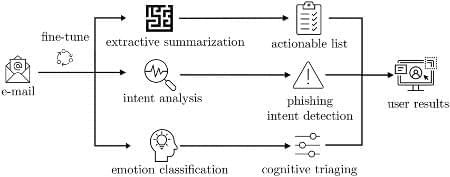
Researchers at Monash University and CSIRO’s Data61 in Australia have recently developed a machine learning-based approach that could help users to identify phishing emails, so that they don’t inadvertently install malware or send sensitive data to cyber-criminals. This model was introduced in a paper pre-published on arXiv and set to be presented at AsiaCCS 2022, a cyber-security conference.
“We have identified a gap in current phishing research, namely realizing that existing literature focuses on rigorous ‘black and white’ methods to classify whether something is a phishing email or not,” Tingmin (Tina) Wu, one of the researchers who carried out the study, told TechXplore.